Category: Networking
Bulk Domain Availability Check via CLI (Bash + Python Only)
You have a list of 50 domain name ideas. Maybe you are launching a product, picking a brand, or trying to find something halfway decent that has not already been squatted. Whatever the reason, typing them one at a time into a registrar search box is not a workflow, it is punishment. This post shows […]
Read more →AWS Security Group Hardening Using VPC Flow Log Analysis: Introducing sg-tightener
Andrew Baker, Group CIO, Capitec Bank Most enterprises did not move to AWS. They extended into it. The datacenter did not go away. The VPN did not go away. The network team provisioned the Direct Connect, someone wrote a security group rule permitting the entire datacenter subnet, and that rule has been sitting there ever […]
Read more →QUIC: The Protocol That Breaks Your Site Without Warning
Why It Exists, What It Gets Wrong, and How to Diagnose and Fix It Andrew Baker · andrewbaker.ninja · 2 May 2026 1. Why TCP Was a Problem QUIC is a complete replacement for the TCP transport layer. To understand why that replacement was necessary, you need to understand what TCP does internally and where […]
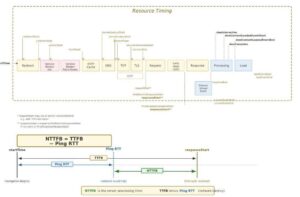
Read more →NTTFB: Net Time to First Byte Explained and Why It Matters
Andrew Baker · February 2026 · andrewbaker.ninja 1 The Problem with TTFB Time to First Byte has been the go to diagnostic for server responsiveness since the early days of web performance engineering. Google’s own web.dev guidance describes TTFB as measuring the elapsed time between the start of navigation and when the first byte of […]
Read more →Cloudflare Free Tier Review: Why It Works for Enterprise
By Andrew Baker, CIO at Capitec Bank There is a truth that most technology vendors either do not understand or choose to ignore: the best sales pitch you will ever make is letting someone use your product for free. Not a watered-down demo, not a 14-day trial that expires before anyone has figured out the […]
Read more →What Is My IP Address? IPv4 Explained for Beginners
Firstly, let me acknowledge that there are lots of these kinds of posts on the internet. But the reason why i wrote this blog is that I wanted to force myself to consolidate the various articles I have read and my learnt knowledge in this space. I will probably update this article several times and […]
Read more →Dublin Traceroute on macOS: Install & Usage Guide
Modern networks are far more complex than the simple point to point paths of the early internet. Equal Cost Multi Path (ECMP) routing, carrier grade NAT, and load balancing mean that packets from your machine to a destination might traverse entirely different network paths depending on flow hashing algorithms. Traditional traceroute tools simply cannot handle […]
Read more →iperf3 Guide: Top 10 Network Performance Testing Use Cases
When something is “slow” on a network, opinions arrive before evidence. Storage teams blame the network, network teams blame the application, and application teams blame “the cloud”.☁️ iperf3 cuts through that noise by giving you hard, repeatable, protocol-level facts about throughput, latency behavior, and packet loss. This post explains what iperf3 actually measures, how it […]
Read more →Rubrik Architecture: Why Restore, Not Backup, Is the Product
1. Backups Should Be Boring (and That Is the Point) Backups are boring. They should be boring. A backup system that generates excitement is usually signalling failure. The only time backups become interesting is when they are missing, and that interest level is lethal. Emergency bridges. Frozen change windows. Executive escalation. Media briefings. Regulatory apology […]
Read more →Test HTTP/2 Max Concurrent Streams: Tools & Guide
1. Introduction Understanding and testing your server’s maximum concurrent stream configuration is critical for both performance tuning and security hardening against HTTP/2 attacks. This guide provides comprehensive tools and techniques to test the SETTINGS_MAX_CONCURRENT_STREAMS parameter on your web servers. This article complements our previous guide on Testing Your Website for HTTP/2 Rapid Reset Vulnerabilities from […]
Read more →