Category: Internet
Test HTTP/2 Max Concurrent Streams: Tools & Guide
1. Introduction Understanding and testing your server’s maximum concurrent stream configuration is critical for both performance tuning and security hardening against HTTP/2 attacks. This guide provides comprehensive tools and techniques to test the SETTINGS_MAX_CONCURRENT_STREAMS parameter on your web servers. This article complements our previous guide on Testing Your Website for HTTP/2 Rapid Reset Vulnerabilities from […]
Read more →Browser Curl with Playwright: Load Testing Guide
Modern sites often block plain curl. Using a real browser engine (Chromium via Playwright) gives you true browser behavior: real TLS/HTTP2 stack, cookies, redirects, and JavaScript execution if needed. This post mirrors the functionality of the original browser_curl.sh wrapper but implemented with Playwright. It also includes an optional Selenium mini-variant at the end. What this […]
Read more →How to Find and Set the MTU on Windows (Step-by-Step)
If you have just changed ISPs or moved house and your internet suddenly starts misbehaving the likelihood is your Maximum Transmission Unit (MTU) is set too high for your ISP. The default internet facing MTU is 1500 bytes, BUT depending on your setup, this often needs to be set much lower. Step 1: First check […]
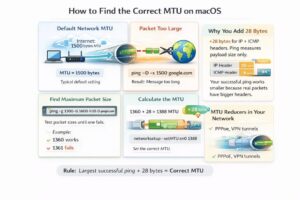
Read more →How to Find and Set the Optimal MTU on Mac/macOS
If you have just changed ISPs or moved house and your internet suddenly starts misbehaving the likelihood is your Maximum Transmission Unit (MTU) is set too high for your ISP. The default internet facing MTU is 1500 bytes, BUT depending on your setup, this often needs to be set much lower. Step 1: First check […]
Read more →