Author: Andrew Baker
Test HTTP/2 Max Concurrent Streams: Tools & Guide
1. Introduction Understanding and testing your server’s maximum concurrent stream configuration is critical for both performance tuning and security hardening against HTTP/2 attacks. This guide provides comprehensive tools and techniques to test the SETTINGS_MAX_CONCURRENT_STREAMS parameter on your web servers. This article complements our previous guide on Testing Your Website for HTTP/2 Rapid Reset Vulnerabilities from […]
Read more →HTTP/2 Rapid Reset CVE-2023-44487: Test Your Server on macOS
Introduction In August 2023, a critical zero day vulnerability in the HTTP/2 protocol was disclosed that affected virtually every HTTP/2 capable web server and proxy. Known as HTTP/2 Rapid Reset (CVE 2023 44487), this vulnerability enabled attackers to launch devastating Distributed Denial of Service (DDoS) attacks with minimal resources. Google reported mitigating the largest DDoS […]
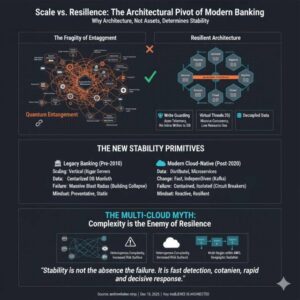
Read more →Why Bank Architecture Determines Resilience More Than Size
1. Size Was Once Mistaken for Stability For most of modern banking history, stability was assumed to increase with size. The thinking was the bigger you are, the more you should care, the more resources you can apply to problems. Larger banks had more capital, more infrastructure, and more people. In a pre-cloud world, this […]
Read more →OSPF vs Human Workload Routing: A Technical Guide
1. Introduction In networking, OSPF (Open Shortest Path First) is a routing protocol that ensures traffic flows along the shortest and lowest cost path through a network. It does not care about hierarchy, seniority, or intent. It routes based on capability, cost, and reliability. Modern engineering organisations behave in exactly the same way, whether they […]
Read more →Java 25 Virtual Threads: Lightweight Concurrency Guide
1. Introduction Java’s concurrency model has undergone a revolutionary transformation with the introduction of Virtual Threads in Java 19 (as a preview feature) and their stabilization in Java 21. With Java 25, virtual threads have reached new levels of maturity by addressing critical pinning issues that previously limited their effectiveness. This article explores the evolution […]
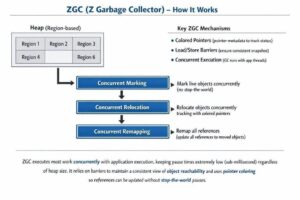
Read more →Pauseless Garbage Collection in Java 25: ZGC Guide
1. Introduction Garbage collection has long been both a blessing and a curse in Java development. While automatic memory management frees developers from manual allocation and deallocation, traditional garbage collectors introduced unpredictable stop the world pauses that could severely impact application responsiveness. For latency sensitive applications such as high frequency trading systems, real time analytics, […]
Read more →Memgraph & Claude Desktop: Detect Mule Accounts on macOS
1. Introduction This guide walks you through setting up Memgraph with Claude Desktop on your laptop to analyze relationships between mule accounts in banking systems. By the end of this tutorial, you’ll have a working setup where Claude can query and visualize banking transaction patterns to identify potential mule account networks. Why Graph Databases for […]
Read more →NMAP + Claude MCP: 20 Vulnerability Scans on macOS
Introduction NMAP (Network Mapper) is one of the most powerful and versatile network scanning tools available for security professionals, system administrators, and ethical hackers. When combined with Claude through the Model Context Protocol (MCP), it becomes an even more powerful tool, allowing you to leverage AI to intelligently analyze scan results, suggest scanning strategies, and […]
Read more →PostgreSQL Prepared Statements: Fix Plan Caching Memory Issues
Prepared statements are one of PostgreSQL’s most powerful features for query optimization. By parsing and planning queries once, then reusing those plans for subsequent executions, they can dramatically improve performance. But this optimization comes with a hidden danger: sometimes caching the same plan for every execution can lead to catastrophic memory exhaustion and performance degradation. […]
Read more →Stablecoins Explained: Types, Uses & How They Move Money
1. What Are Stablecoins? Stablecoins are a type of cryptocurrency designed to maintain a stable value by pegging themselves to a reserve asset, typically a fiat currency like the US dollar. Unlike volatile cryptocurrencies such as Bitcoin or Ethereum, which can experience dramatic price swings, stablecoins aim to provide the benefits of digital currency without […]
Read more →