Category: Banking + Cyber
Cloudflare Free Tier Review: Why It Works for Enterprise
By Andrew Baker, CIO at Capitec Bank There is a truth that most technology vendors either do not understand or choose to ignore: the best sales pitch you will ever make is letting someone use your product for free. Not a watered-down demo, not a 14-day trial that expires before anyone has figured out the […]
Read more →WordPress XMLRPC.PHP Brute Force Testing Guide for macOS
A Comprehensive Security Testing Guide for Mac Users 1. Introduction WordPress xmlrpc.php is a legacy XML-RPC interface that enables remote connections to your WordPress site. While designed for legitimate integrations, this endpoint has become a major security concern due to its susceptibility to brute force attacks and amplification attacks. Understanding how to test your WordPress […]
Read more →Banking Complexity: Leadership Failure or Inevitable Growth?
If you look back over time at all once great companies, you will see that eventually simplicity gave way to scale. What are some of the risks that drive this? This is where many great banks lose their edge. But is this really a shared destiny for all banks, or did the leadership simply fail […]
Read more →Protected: Neo by Capitec: AI Client Support That Resolves Issues Proactively
There is no excerpt because this is a protected post.
Read more →Rubrik Architecture: Why Restore, Not Backup, Is the Product
1. Backups Should Be Boring (and That Is the Point) Backups are boring. They should be boring. A backup system that generates excitement is usually signalling failure. The only time backups become interesting is when they are missing, and that interest level is lethal. Emergency bridges. Frozen change windows. Executive escalation. Media briefings. Regulatory apology […]
Read more →South Africa Banking Consolidation: Costs, Pressure & Trends
I wanted to write about the trends we can see playing out, both in South Africa and globally with respect to: Large Retailers, Mobile Networks, Banking, Insurance and Technology. These thoughts are my own and I am often wrong, so dont get too excited if you dont agree with me 🙂 South Africa is experiencing […]
Read more →CVE-2024-3094: Detecting the XZ Utils SSH Backdoor
Executive Summary CVE-2024-3094 represents one of the most sophisticated supply chain attacks in recent history. Discovered in March 2024, this vulnerability embedded a backdoor into XZ Utils versions 5.6.0 and 5.6.1, allowing attackers to compromise SSH authentication on Linux systems. With a CVSS score of 10.0 (Critical), this attack demonstrates the extreme risks inherent in […]
Read more →HTTP/2 Rapid Reset CVE-2023-44487: Test Your Server on macOS
Introduction In August 2023, a critical zero day vulnerability in the HTTP/2 protocol was disclosed that affected virtually every HTTP/2 capable web server and proxy. Known as HTTP/2 Rapid Reset (CVE 2023 44487), this vulnerability enabled attackers to launch devastating Distributed Denial of Service (DDoS) attacks with minimal resources. Google reported mitigating the largest DDoS […]
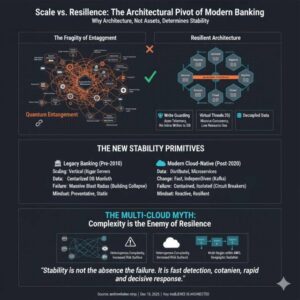
Read more →Why Bank Architecture Determines Resilience More Than Size
1. Size Was Once Mistaken for Stability For most of modern banking history, stability was assumed to increase with size. The thinking was the bigger you are, the more you should care, the more resources you can apply to problems. Larger banks had more capital, more infrastructure, and more people. In a pre-cloud world, this […]
Read more →Memgraph & Claude Desktop: Detect Mule Accounts on macOS
1. Introduction This guide walks you through setting up Memgraph with Claude Desktop on your laptop to analyze relationships between mule accounts in banking systems. By the end of this tutorial, you’ll have a working setup where Claude can query and visualize banking transaction patterns to identify potential mule account networks. Why Graph Databases for […]
Read more →