Category: Technology
Know Your System: The Operational Cognition Questionnaire
Most outages are not caused by a single bug. They are caused by teams that have gradually lost a coherent mental model of the system they operate. Kubernetes retries. Queues absorb backpressure. Auto scaling masks inefficiency. Managed services hide infrastructure complexity. Over time, teams begin operating systems they no longer fully understand. Then something breaks. […]
Read more →Why Visible Technology Leaders Build More Trust Than Silent Ones
1. The Corporate Voice Is Losing Credibility A strange thing is happening in executive communication. The more polished it becomes, the less believable it feels. For years, large organizations trained executives to communicate through multiple layers of lawyers, communications teams, governance forums, media handlers, and reputation specialists. Every statement became progressively safer, flatter, and more […]
Read more →Psychopathic Systems: Why Catastrophic Outages Are Never Accidents
Catastrophic system outages are never purely accidental because the conditions enabling them accumulate quietly over time, embedded within organizational structures, incentive misalignments, and suppressed warning signals. Like destructive human behaviour, systemic failure reveals latent dysfunction that existed long before the visible collapse, suggesting every major outage is ultimately a predictable consequence of chronic, overlooked vulnerabilities. […]
Read more →The Legacy Choice: Why x86 in the Data Centre Is Now an Expensive Decision, Not a Default
The economics crossed the tipping point quietly. Most enterprises missed it. The ones who noticed are not going back. 1. How Defaults Become Legacy Every technology that eventually becomes legacy spent years being the obvious choice. Nobody chose x86 over anything. It was simply there, it worked, the tooling was built around it, the hiring […]
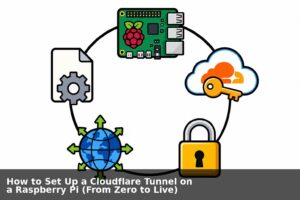
Read more →How to Set Up a Cloudflare Tunnel on a Raspberry Pi (From Zero to Live)
Goal: Expose a service running on your Raspberry Pi to the public internet, securely, without port-forwarding or a static IP, using Cloudflare Tunnel. What You’ll End Up With Prerequisites Requirement Notes Raspberry Pi (any model) Running Raspberry Pi OS (64-bit recommended) A domain name e.g. yourdomain.com purchased anywhere (Namecheap, GoDaddy, etc.) SSH access to the […]
Read more →pi2s3: An AMI for Your Raspberry Pi
If you have ever had a Raspberry Pi die on you, you know exactly what the recovery process looks like. You flash a new SD card or NVMe, reinstall your packages, rebuild your Docker stacks, reconnect your Cloudflare tunnel, reconfigure nginx, re-enter your credentials, clone your repos, tweak your cron jobs, and spend the better […]
Read more →Migrating a Pi 5 WordPress Stack from SD Card to NVMe
I run a full WordPress stack on a Raspberry Pi 5 sitting on my desk: MariaDB, PHP-FPM, Nginx, and Redis, all inside Docker containers, served publicly through a Cloudflare tunnel. After fitting an NVMe SSD via the Pi 5 HAT+, the obvious next step was getting Docker off the SD card entirely. The SD card […]
Read more →Fix Raspberry Pi Boot Failures: SD to NVMe in 5 Steps
A real-world guide to making your Pi bulletproof, from SD card corruption to NVMe migration I learned this lesson the hard way. My Raspberry Pi 5 was happily serving a production WordPress site when I rebooted it. Two minutes later there was no SSH, no site, just a solid red light staring back at me. […]
Read more →Why Tech Empires Fall: Arrogance, Control & Collapse
1. Arrogance Is the Drawbridge Every great empire in history has been brought low by a version of the same mistake. The fortress is so strong, the moat so wide, and the walls so high, that the people inside begin to believe they have transcended the rules. They stop serving the people beyond the walls. […]
Read more →Why Core Banking Architecture Has Always Been Flawed
The COBOL apocalypse conversation this week has been useful, because it has forced the industry to confront something it has been avoiding for decades. But most of the coverage is stopping at the wrong point. Everyone is talking about COBOL. Nobody is talking about the architectural philosophy that COBOL gave birth to, the one that […]
Read more →