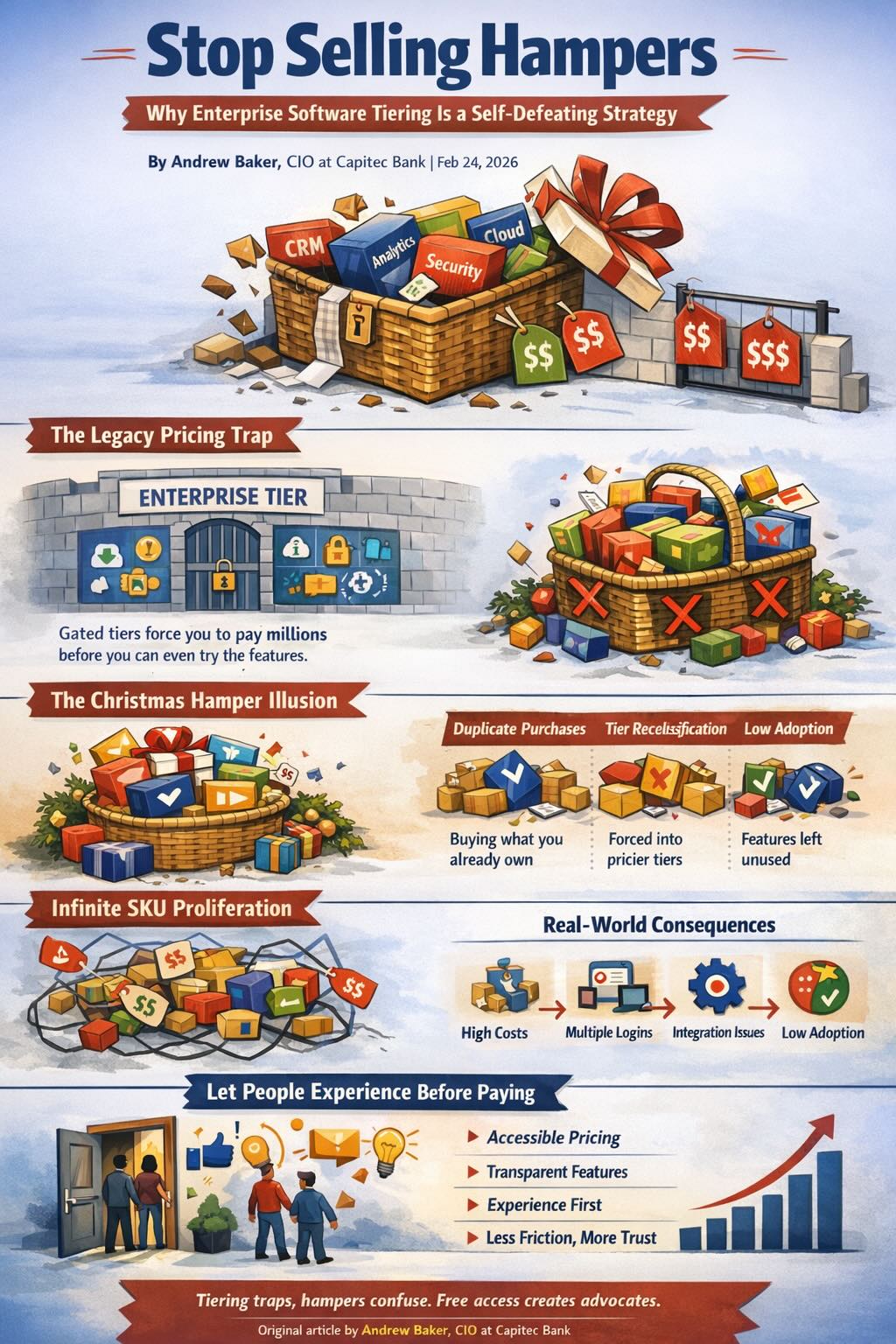
Stop Selling Hampers: Why Enterprise Software Tiering Is a Self-Defeating Strategy
By Andrew Baker, CIO at Capitec Bank
There is a category of enterprise technology vendor whose approach to pricing is so fundamentally at odds with how purchasing decisions actually get made that it borders on self-defeating. Their commercial model is built on access gates, bundled tiers, and a deeply held belief that controlling what a customer can see before they pay is a form of leverage. It is not. It is anti-sales dressed up as a pricing strategy, and a generational reckoning is coming for every vendor that has not figured this out yet.
1. The Legacy Pricing Trap
You know the vendors I mean even if I will not name them here. Their pricing model is built on tiers, each one separated from the next by a gap that costs companies millions of dollars to cross. The product catalogue is divided up such that anything genuinely interesting sits in a tier that requires a significant commercial commitment before you can touch it. You cannot experiment with it. You cannot build intuition about it. You cannot develop the informed advocacy that would eventually lead your organisation to invest in it properly. The gate comes before the experience, and the gate is expensive.
2. The Bundle Illusion
2.1 The Christmas Hamper Problem
Buying enterprise software is nothing like buying a Christmas hamper. With a hamper you are happy saying you are buying “stuff”. You do not need to know what is in it or whether you will use every item. Enterprise technology does not work like that. You cannot tell your board you are buying “stuff” from vendor X, and you cannot tell your CISO that the solution to your identity management problem is definitely somewhere in the tier you just committed millions to. Every product needs to be evaluated, understood, and justified against a specific problem.
Yet the hamper model is precisely what tiered pricing enforces. Inside the bundle are products you actively use, products you decided were not fit for purpose, products you never knew existed until after signing, and products duplicated by something you already own. The vendor’s position is that the bundle is worth the price regardless of how much you consume. They are so magnificent, apparently, that clients should simply pay for the option to use the software.
2.2 The Duplicate Purchase Problem
I have watched this play out repeatedly. Organisations on a pricing tier that included a fully capable security product, who had gone out and bought the same capability from a competitor anyway, because nobody knew the bundled product was there, or had no basis for trusting it when a real problem arrived. The free tier philosophy exists precisely to prevent this. If engineers can experience a product before a commercial commitment is made, they build the knowledge and trust that makes the bundled product the obvious choice rather than the invisible one.
2.3 The Tier Reclassification Trap
It gets worse. These same vendors have a habit of quietly moving products that sit in your current tier up into a higher tier at contract renewal. The feature set you budgeted for and built processes around is now in the next tier up, and the message is clear: pay more or lose capability. The commercial logic from the vendor’s side is understandable in the narrow short-term sense. The strategic damage is severe and largely invisible until it is too late to reverse.
The practical consequence is that customers become genuinely reluctant to adopt new products within their current tier, even when those products are included and theoretically free to use. The rational response to a vendor that periodically reclassifies features upward is to avoid becoming dependent on anything you are not paying explicitly to retain. So the products sit unused. The integration work does not happen. The institutional knowledge does not develop. And the vendor wonders why adoption of their broader portfolio is lower than the addressable opportunity suggests it should be.
2.4 The Refresh Con
The vendor’s response to low adoption of bundled products is not to ask why included products go unused or what that says about product accessibility. It is to restructure the bundle, move items between tiers, throw out the tins of expired spam, and keep the price the same.
The hamper is still worth the same, apparently.
3. The Opposite Problem: Infinite SKU Proliferation
If the hamper vendor’s sin is bundling everything together and hiding it behind a price wall, there is a mirror image failure mode that deserves equal scrutiny: vendors who partition their product so aggressively that the act of purchasing it becomes a liability.
3.1 Everything Is a New Product
Some vendors have discovered that any incremental capability, no matter how basic, can be packaged as a distinct product with its own SKU, its own login portal, its own contract, and its own renewal cycle. Add basic monitoring dashboards to your core platform? That is a new product. Ship a critical security feature that any reasonable customer would consider table stakes? That is an optional add-on. Need audit logging? That will be a separate line item. Need API access to your own data? That is the enterprise tier.
The motivation is understandable from a short-term revenue perspective. Every new product creates a new upsell conversation. Every capability withheld is a future negotiation. But the cumulative effect is a catalogue so fragmented that no single person in your organisation, including the vendor’s own account team, fully understands what a customer has and has not purchased at any given point.
3.2 The Open Source Repackaging Con
A particularly cynical variant of this approach involves vendors who take well-maintained open source projects, wrap a thin commercial layer around them, and sell them back to enterprise customers as premium products. The underlying technology is freely available on GitHub. The vendor has added a logo, a billing system, and perhaps a support contract of debatable quality. The customer, often a non-technical procurement team acting on a vendor briefing, has no idea they are paying a significant annual fee for software they could have deployed themselves.
This is not innovation. It is arbitrage on organisational complexity, and it relies entirely on the purchasing side lacking the technical depth to identify what they are actually buying. When the technical teams find out, the reputational damage to the vendor is significant and difficult to recover from. Trust in enterprise software relationships, once broken by this kind of discovery, rarely fully repairs.
3.3 Harmful Product Combinations
The most operationally dangerous consequence of extreme product partitioning is that it becomes possible for customers to purchase combinations of products that are genuinely inadequate for the problem they are trying to solve. This is not a theoretical risk. It happens routinely when vendors slice their offering finely enough that no single package provides end-to-end coverage of a real-world use case.
This problem reaches its peak severity in the security sector. A customer buys a security product from a well-known vendor. They do a reasonable job of evaluating it. They sign a contract. They deploy it. And then something bad happens, and it turns out that the detection capability, the response capability, and the alerting capability they assumed were part of what they bought are actually three separate products, two of which they did not purchase.
The client will, entirely reasonably, point out that they believed they had bought protection. The vendor will point to the contract language. Both are correct and neither is useful. The outcome is a breach that the product was theoretically capable of preventing but practically did not, because the customer was sold a component when they needed a system.
Security vendors bear a particular responsibility here because the asymmetry of consequence is so severe. A misconfigured analytics platform costs you insight. A misconfigured or incomplete security product costs you everything. Vendors who knowingly design their packaging such that customers can inadvertently purchase inadequate protection are not just making a commercial miscalculation. They are making an ethical one.
3.4 The Fragmentation Tax
Beyond the security risk, extreme product partitioning imposes a significant and largely invisible operational burden on the customer. Multiple contracts. Multiple renewal dates. Multiple login portals. Multiple support relationships. Multiple sets of administrators. Multiple training requirements. The total cost of ownership of a fragmented product suite is consistently higher than any single-vendor analysis will suggest, because the integration costs, the context switching costs, and the organisational overhead of managing dozens of micro-relationships with the same vendor are distributed across departments and never appear in a single budget line.
The vendor sees this as customer stickiness. The customer eventually sees it as a hostage situation.
4. A Generational Reckoning
The generational problem this creates is profound and slow-moving enough that most of these vendors will not feel it until it is structurally very difficult to address. The technology leaders who bought into these platforms did so in an era where the vendor had sufficient market leverage to make the tier-based model stick. Those leaders are gradually retiring. The generation replacing them grew up with AWS free tier, with Cloudflare free tier, with open source everything, with the expectation that you experience a product before you commit to it. They have spent their formative professional years building instincts on platforms that trusted them with real capability before asking for money.
When those leaders sit across a procurement table from a vendor whose pitch begins with a multi-million dollar tier commitment required just to evaluate the relevant product set, the cultural mismatch is immediate and significant. It is not just a price objection. It is a philosophical incompatibility with how they believe technology decisions should be made. And unlike the previous generation of buyers who perhaps had fewer alternatives, this generation has grown up with genuinely competitive options that do not impose the same barriers.
The vendors who have built their commercial model on tier-based access restrictions have a window to adapt. That window is not permanent. Every year that passes without meaningful change to how they allow potential customers to experience their products is another cohort of future decision makers building their instincts and loyalties elsewhere.
The root cause of this strategic blindness is that there is no metric for the depth of understanding your product has in the marketplace. You cannot put it in a board report. You cannot trend it quarter on quarter. You cannot attribute it to a campaign or a sales motion. And because it is unmeasurable, short-sighted technology companies convince themselves the gap can be bridged through other means. So they invest in snappy Gartner acronyms that reframe existing capability as visionary innovation, and they deploy fleets of well-heeled sales teams whose job is to manufacture urgency and compress evaluation cycles before the prospect has time to develop genuine product intuition. It works, right up until it does not. The deal closes but the understanding never develops, and without understanding there is no organic advocacy, no internal champion who truly believes in the platform, and no resilience when the product disappoints.
Technology companies run by engineers tend to understand this instinctively. Engineers know what it means to learn by doing. They know the difference between reading documentation and actually building something. They know that genuine conviction about a technology comes from hands-on experience and cannot be manufactured by a sales process however well resourced. When engineers run product strategy, accessible pricing and free tier investment make intuitive sense because they have lived the experience themselves. When the company is run primarily by people whose mental model of selling is about controlling access and extracting maximum value at each gate, the free tier looks like revenue left on the table rather than pipeline being built. That framing error is expensive, and it compounds over time in ways that do not show up in any dashboard until the generational shift is already well underway.
5. Conclusion
The technology industry has a persistent tendency to over-invest in the proxies for value rather than value itself. Brand recognition, analyst rankings, conference presence, and content marketing are all proxies. They describe a product from a distance. They cannot substitute for the experience of building with it, debugging it at midnight, watching it absorb an attack, or navigating an outage with enough architectural understanding to maintain composure.
The vendors still operating on the hamper model are not just leaving pipeline on the table. They are actively training the next generation of decision makers to build loyalty elsewhere. The vendors operating on the infinite SKU model are doing something arguably worse: they are selling customers the illusion of capability without the substance of it, and in the security domain that distinction carries consequences that no contract clause can fully mitigate.
The ask is simple. Stop selling hampers. Stop selling fragments. Start selling products. Price them in a way that lets people touch them before they commit to them. Package them in a way that ensures a customer who buys your security product actually has security. Trust that what you have built is good enough to demonstrate its own value. If it is not, that is the more important problem to solve.
Andrew Baker is the Chief Information Officer at Capitec Bank in South Africa. He writes about enterprise architecture, cloud infrastructure, banking technology, and leadership at andrewbaker.ninja.